10 Fortigate 80F Secrets For Better Security
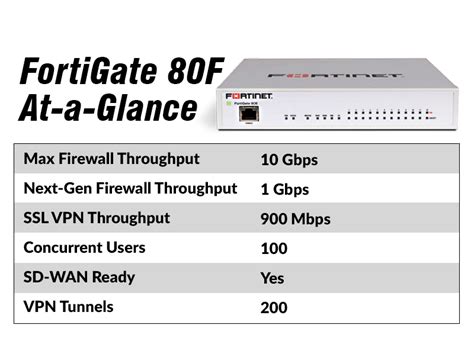
The FortiGate 80F is a powerful and feature-rich network security appliance designed to provide advanced threat protection, secure connectivity, and improved network performance. As a security expert, it's essential to understand the capabilities and configuration options of this device to maximize its potential and ensure better security for your network. In this article, we'll delve into 10 FortiGate 80F secrets that can help you optimize your security posture and get the most out of your investment.
Understanding the FortiGate 80F Architecture
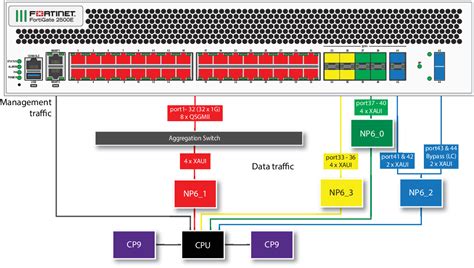
The FortiGate 80F is built on a purpose-built architecture that integrates a range of security functions, including firewall, VPN, intrusion prevention, and antivirus. To fully leverage the capabilities of this device, it’s crucial to understand its architecture and how the different components work together to provide comprehensive security. Key components of the FortiGate 80F include the FortiOS operating system, which provides a robust and secure platform for configuring and managing the device.
Configuring Firewall Policies
Firewall policies are a critical aspect of network security, and the FortiGate 80F provides a range of options for configuring and managing these policies. To create effective firewall policies, you need to understand the different policy modes, including NAT, route, and transparent mode. You should also be familiar with the policy syntax and how to use objects and address groups to simplify policy configuration.
| Policy Mode | Description |
|---|---|
| NAT Mode | Network address translation mode, which allows multiple devices to share a single public IP address |
| Route Mode | Route mode, which provides layer 3 routing capabilities |
| Transparent Mode | Transparent mode, which allows the FortiGate to operate as a layer 2 device |
Optimizing Threat Protection

The FortiGate 80F provides a range of threat protection features, including intrusion prevention, antivirus, and web filtering. To optimize threat protection, you should configure these features to work together seamlessly. This includes enabling the relevant features, configuring policies, and tuning settings to meet your specific security needs.
Using SSL/TLS Inspection
SSL/TLS inspection is a critical feature that allows the FortiGate 80F to inspect encrypted traffic for threats. To use SSL/TLS inspection effectively, you need to enable the feature, configure certificates, and tune settings to optimize performance. You should also be aware of the potential impact on network performance and take steps to minimize any adverse effects.
- Enable SSL/TLS inspection to detect threats in encrypted traffic
- Configure certificates to establish trust with your network devices
- Tune settings to optimize performance and minimize impact on network traffic
Implementing Secure Connectivity
The FortiGate 80F provides a range of features to support secure connectivity, including VPN and SSL/TLS encryption. To implement secure connectivity, you should configure VPN settings, establish trust with your network devices, and monitor network traffic to detect potential threats.
Configuring VPN Settings
Configuring VPN settings is a critical aspect of implementing secure connectivity. You should choose the right VPN protocol, configure encryption settings, and establish trust with your network devices. You should also be aware of the potential impact on network performance and take steps to minimize any adverse effects.
| VPN Protocol | Description |
|---|---|
| IPSec | Internet Protocol Security, which provides encryption and authentication for IP traffic |
| SSL/TLS | Secure Sockets Layer/Transport Layer Security, which provides encryption and authentication for web traffic |
What is the FortiGate 80F?
+The FortiGate 80F is a network security appliance designed to provide advanced threat protection, secure connectivity, and improved network performance.
How do I configure firewall policies on the FortiGate 80F?
+To configure firewall policies on the FortiGate 80F, you need to understand the different policy modes, including NAT, route, and transparent mode. You should also be familiar with the policy syntax and how to use objects and address groups to simplify policy configuration.
What is SSL/TLS inspection, and how does it work?
+SSL/TLS inspection is a feature that allows the FortiGate 80F to inspect encrypted traffic for threats. It works by decrypting the traffic, inspecting it for threats, and then re-encrypting it before forwarding it to its destination.